Solving Web400 Challenge
Accessed the Web4 challenge and we are given a new Hint!. hints are back!! 🙂
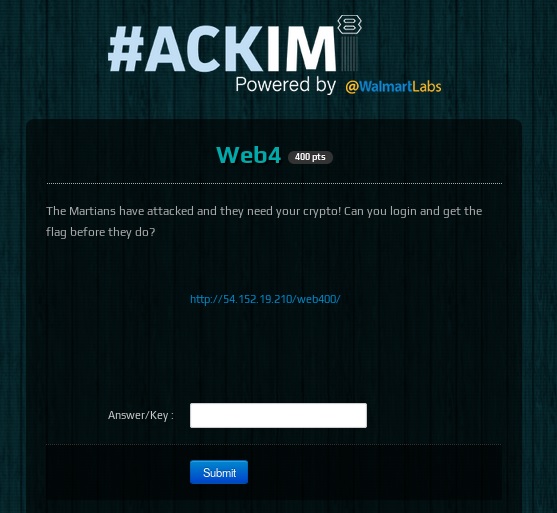
Possibly a crypto challenge ahead from a martian!?.. Right, so going into the link we find that there a captcha along with a login.

View source gives away the “partial” password and its 69 characters long. Also, there appears to be a backup of SQL file somewhere in the server. Meaning some interesting DB file should be directly reference in the /web400/ path. I tried a couple of combinations before getting “database.sql” file as a download
On closer evaluation of this file, it appears there is a user named “Jaffa” and password hash is also present in this DB. The Password has variable hinted bcrypt, being used.
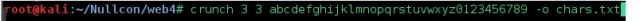
So now the martian crypto challenge has presented itself. It appears that we needed “3” more characters as hinted by Null team, via twitter. And the reasoning behind this is that there is a Maximum length to a password done using bcrypt ->72 characters.
Used crunch to create a dictionary of all the characters using the existing character sequence [a-z 0-9], with following command.
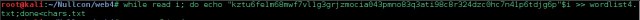
Appended the “partial password” to the chars created by crunch.
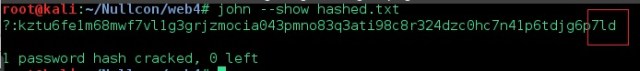
And then used john to crack the password using the newly created wordlist
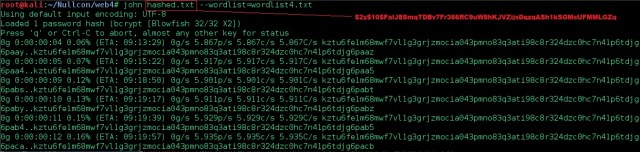
It took quite sometime.. and finally got the last three characters for the password and login with user “jaffa” to get the flag for web400 challenge.