Solving a CTF is like addiction, you can’t possibly stop at 1. So i tried to submit the flag and it failed. There was a syntax to follow flag {…}. This was not very intuitive for me and there was a tweet from the nullcon handle. 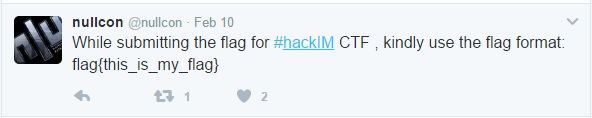
Solving Web200 Challenge!
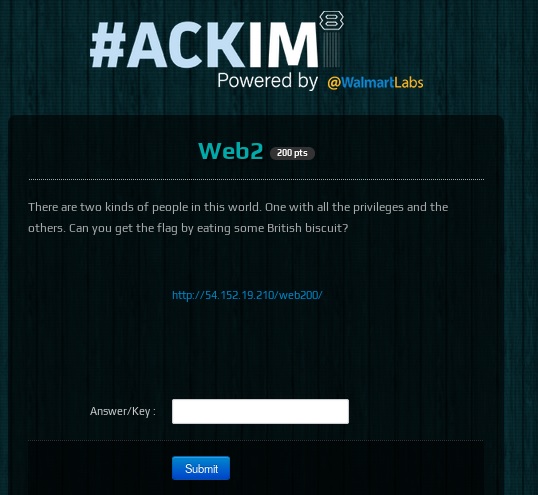
So, the hint seems to indicate some aspect of users privileges and also something to do with the cookie.

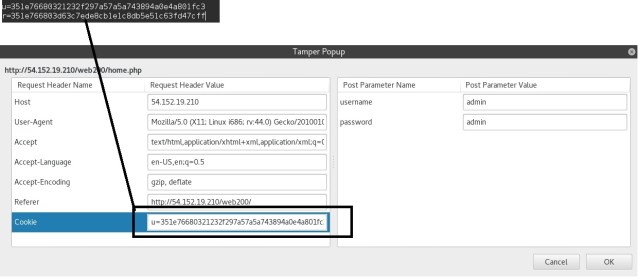
Tried accessing the page with admin/admin and to my surprise, although we could get it. Stated “You do not possess enough power, Try Harder!” in the next page. So i reviewed the cookie field using tamper data and it had 2 values. U -> which seems to hint “user?” and “R”-> which seems to hint “Rights”?.. This was my assumption
The page also allowed creating of users and had a registration page. So i created a couple of users to figure out what the logic could be for creating /cough baking a British Biscuit!.

It appeared that value “351e766803” was a hard-coded value appended to a hash for both the fields and the “Rights” -> R field was common for all users.
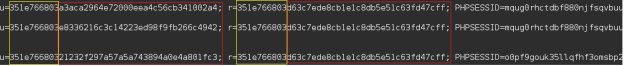
So i looked up what “21232f297a57a5a743894a0e4a801fc3” meant, it was simply the MD5 hash for the username admin in md5(‘admin’) format.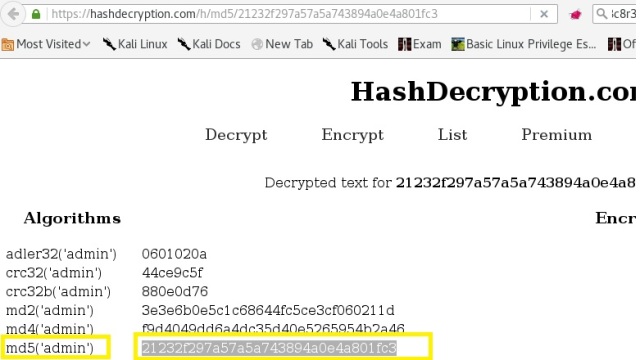
So that must be it!.. the Rights -> R field should be also “admin” to get “powers”. So replacing this value with the plugin tamper data, gave me the flag!! 2 flags Down!!
