NullCon 2017 is in the corner, Feb 28th – March 02. It has some really good talks, workshops and training’s lined up with many industry experts from around the world. Another note about NullCon is the CTF before Nullcon. Often hosted over ctf.nullcon.net. This time i participated in the web challenges and got upto web400.
For the folks new to the concept of a CTF – Capture the flag – wargame, as Wikipedia coins the term, is a tournament held by experts in the industry with some objectives related to – Crypto, Reversing, Exploitation and Web Applications and there is a hidden flag within that application/challenge which is only accessible after solving a specific challenge successfully.A Simple CTF walk-through( Hack.me ), was my previous post and i should have added some introduction to my write up. I’m quite sure the method i went about was not optimal and there are better ways to going about it. Nonetheless, this write-up should give you a good idea on how the web based challenges function.
Solving Web100 Challenge!

On accessing the first web challenge there was message about Chris Martin. He is the singer /co-founder of ColdPlay. I love their music and so i tuned into a YouTube channel by this band 🙂 .
There was a login screen and i tried user:Chris and Pass:ColdPlay, So original.. right. I got an output stating that the IP was “logged”. This application, could be using the X-Forwarded-For header is what came to mind. That is the right way to identify the “true” client IP addresses in case of access of this system from behind a proxy.

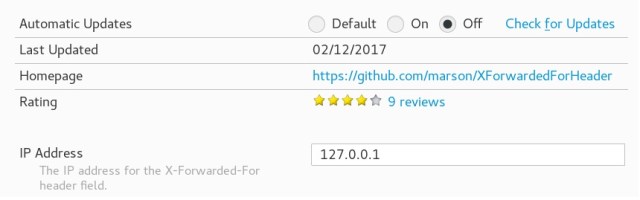
Next step was to use a Addon (X-Forwarded-For, for firefox) that can add this header in the request to mimic the original source. So what should be the IP address? “Chris wanted to go home”. Home possibly meant -127.0.0.1 so added that as a header within the plugin as following. The older credential did not work.
So i went into viewing source. There was a commented line, which appeared to be base64 at the end of the source.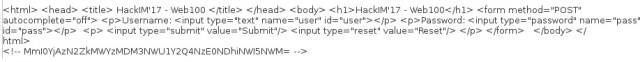
Decoded this base 64 and it looked like an md5sum and googled for it. There were many colplay references being used as a playlist. But no reference to a hash being cracked.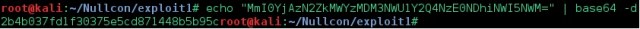
The characters from within the google search that appeared were an exact match.
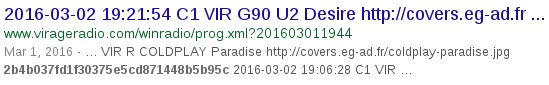
So this is the right path, i thought to myself and then proceeded to use user: colplay and password: paradise and that was it! Flag!!!
